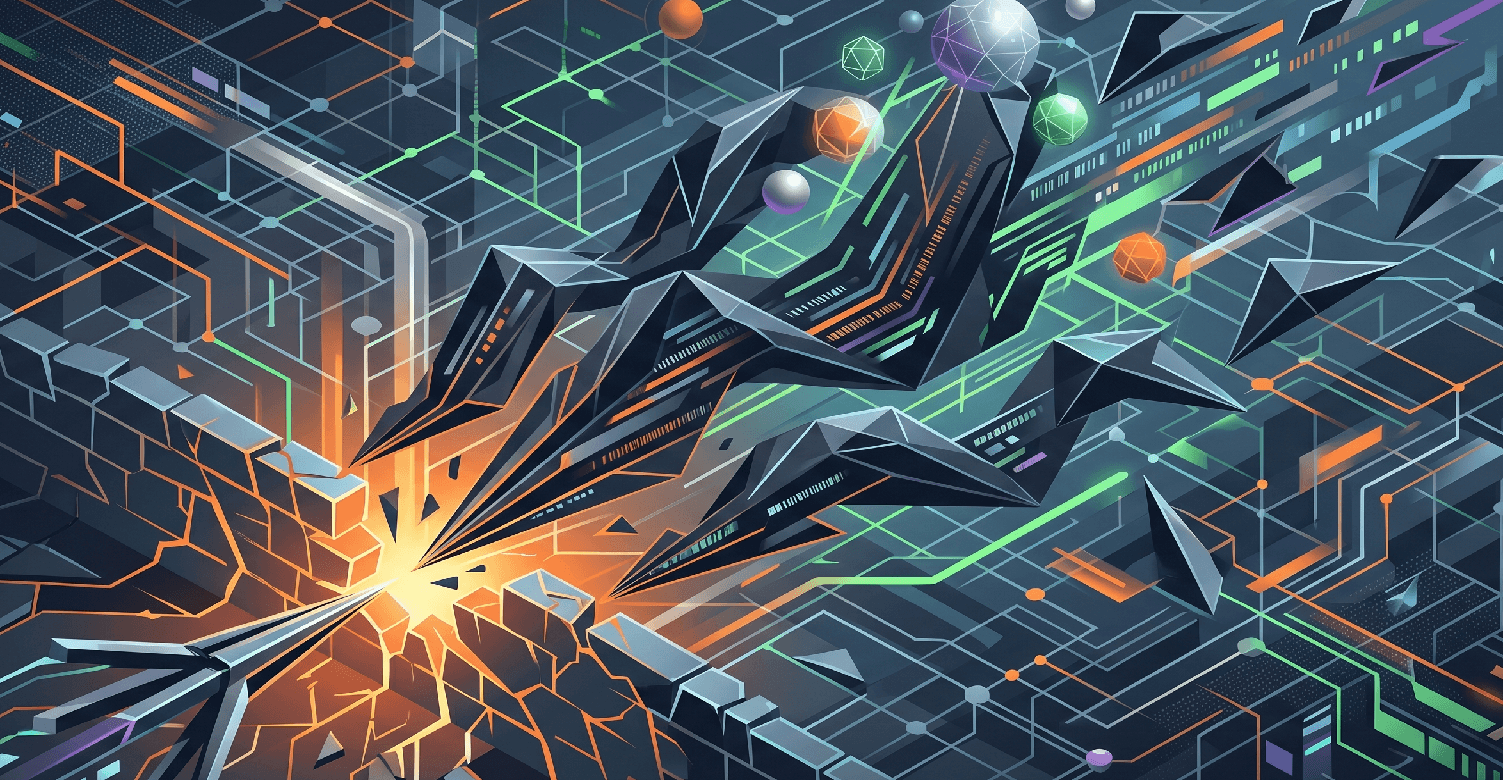
The cyber threat landscape in 2026 is so different to 3 years back, where the core motivation of attackers, be it financial, geopolitical, or purely destructive, is the same, the methods have undergone a profound and rapid transformation.
Traditional, perimeter-focused security models have been systematically dismantled by a new generation of attacks that are faster, more evasive, and harder to detect. The key differentiator in this new era is the intelligent, scaled application of Artificial Intelligence (AI) and automated data analysis by the attackers themselves.
To understand how to defend against these sophisticated threats, we need to look at where the next wave of attack techniques is originating. Organisations like the SANS Institute have long been a credible voice in threat intelligence, providing crucial industry foresight. Their forecast of the 🔗Top 5 Most Dangerous New Attack Techniques serves as a warning and a reference point for forward-thinking security professionals.
This foresight isn’t an isolated prediction but a direct result of observing real-world trends. Our take on this unpacks the key theme.
Ever-changing Threats
The new breed of attack is defined not by novelty for its own sake, but by high-fidelity automation and surgical precision. Attackers are no longer just casting wide, random nets; they’re building adaptive, learning-based systems to identify and exploit specific, high-value vulnerabilities.
Traditional defenses are often caught in a reactive cycle which involves patching after a breach or adding new tools. In 2026, this approach might not be enough, there might need to be a healthy dose of proactive defence in the mix.
High-Priority Emerging Techniques
Many attack vector categories are familiar but their sophistication is a game-changer. The SANS RSAC 2026 list highlights techniques that demand immediate attention and strategic re-evaluation. Based on current trends, we need to look at a few key areas:
1. Deepfake-Driven Social Engineering at Scale
This technique leverages mature Generative AI (GenAI) models, including Large Video and Voice Synthesis models, to create hyper-realistic, real-time personas of trusted individuals. Attackers can simulate a conversation with a C-suite executive, a key vendor, or even a direct manager to bypass traditional multifactor authentication (MFA) challenges and trick staff into approving large financial transactions or downloading malicious code. This is BEC 2.0. The human eye and ear are no longer reliable primary verification tools.
2. Adversarial AI and Data Manipulation
Perhaps the most insidious new technique is the manipulation of the very AI systems an organisation relies on. This involves poisoning a company’s own internal data models (like those used for internal data classification, network anomaly detection, or even automated customer support bots) with subtle malicious data. This data then creates backdoors, causes the AI to ignore malicious traffic, or to perform harmful actions that seem legitimate. Attacking into AI systems is a core future threat.
3. AI-Generated Polymorphic Malware
Traditional signature-based antivirus is useless against this threat. AI-powered malware code automatically creates hundreds of subtly different, uniquely evasive versions of itself for every unique target. Each variant has a new ‘signature’ that a classic scanner has never seen before. These variants adapt their code in real-time based on the defensive tools they encounter, making them almost impossible to block using traditional static analysis.
Data-Led Defence
The speed and volume of these new AI-powered attacks have surpassed human cognitive limits. An analyst looking at thousands of alerts can miss the crucial signal amidst the noise. In 2026, detection must be as automated as attack. This is where the intersection of human expertise and advanced tools is critical. A successful defence now requires:
Real-Time Data Analysis |
Processing entire data streams, not just log summaries. |
Continuous Compliance |
Proactively verifying that security controls are effective, all the time, rather than relying on point-in-time audits. |
AI-Powered Detection Systems |
Employing automated systems capable of identifying and responding to zero-day, polymorphic threats at machine speed. |
Contextual Intelligence |
Deep analysis of data to understand why a set of actions is malicious, rather than just what happened. |
Building Cyber Resilience
Education and process are as vital as technology. True resilience comes from a multi-layered approach that empowers well-trained people with the best informed tools. This is the ethos that Mondas is built on. We combine a leading team, including specialists in data science and AI security, with best-in-class software and platforms that process data globally to build adaptive, predictive defences. We’re always striving to move from cyber defence to cyber resilience for our clients.
Proactive Steps
While the challenge is complex, your first steps should be clear and focused on data integrity:
- Re-Evaluate Human Verification Processes
Implement strict multi-channel verification for high-value requests (financial or access-related) that are independent of digital channels (e.g., a known phone number from a different device). - Conduct an AI Audit
Identify every AI tool used in your organisation (external or internal). Assess who provides its data and what safeguards are in place against data poisoning. - Prioritise Behavioral Analytics over Signatures
Invest in endpoint and network detection systems that prioritise anomalous behavioral patterns over fixed signatures, to better detect polymorphic threats.
Mondas specialises in these issues, leveraging a blend of human expert insight and advanced AI-powered data analysis to keep businesses resilient against emerging threats.
If you are struggling with the complex and changing issues outlined in this article, or need help auditing your own use of AI for security, contact us today to explore how Mondas can build a bespoke, data-led defence strategy for your organisation.
Author: Lance Nevill, Cyber Security Director. Lance focuses on strategic threat analysis and translating technical vulnerability into business risk. Connect with Lance on LinkedIn: 🔗https://uk.linkedin.com/in/lancenevill
Article first published: 16/04/2026